The internet is an unsecured network; we are constantly under attack from hackers and botnets. This means someone can easily spoof or spy on our online activity. Therefore, if you are security-conscious, you should always be on the lookout for tools like VPNs and Proxies.
But which one is better, VPN or Proxy? This is the most common question when it comes to hiding the IP Address. Since both of them have their advantages and disadvantages. However, this article will help you make a quick selection between VPNs and proxies.
VPN or Proxy (How to Use & Best for Mac)
Why Do We Compare Proxy Servers And VPNs? Right now, it’s best to understand why we should compare the VPN and proxy servers in the first place. The first and foremost reason is they work on the customary goal; both hide IP Addresses when you visit a website.
So when you enter unauthorized websites, they aim to register your location using the IP Address. Proxy and VPN will hide the information since it gives its IP Address rather than your device.
However, why a device owner wants to hide an IP address depends on what the users want to achieve. And this is what VPN vs Proxy comes across the internet; as of now, they both work on the same entity.
Proxy Vs. VPN: Which One Is Better?
The table below will help you determine which is better: VPN or Proxy for Mac users.
| Parameter | VPN | Proxy |
| IP Address | Completely invisible | Hides, but proxy severs can spy |
| Encryption | It includes strict encryption level | It includes mid-level or no of encryption level |
| Speed | Offers rapid speed | Varies of type of proxy sever |
| Connection | It offers stable and seamless connection | Sometimes it can wrong play |
| Price | Costly | Free |
| Streaming | Highly preferred | Not preferred |
| Integration | The VPN are always designed for personal use. Integration is done just with few clicks. | The integration process is quite tough. |
| Purpose | Mostly oriented for single client. | Oriented for the business purpose to gather the information. |
| Encryption | Smartly encrypts your traffic | Don’t encrypt your traffic |
| Reliability | More reliable | Less reliable |
| Working Model | Works on OS level | Works on application level |
| Use | Easy to use | Complicated to use |
| Good For Streaming | Yes | Partially good, as it only bypass proxy blocks |
Where Proxy Server Useful
If you are willing to access the data over the geographical region and aren’t bothering to hide your data anymore, there is nothing wrong with using the proxy server. Currently, some proxy servers are available at no cost and can be accessed from any computer or device.
However, they aren’t as good as a VPN if privacy is the primary concern. For instance, if you are working on corporate projects, don’t try using the VPN.
Where VPN Useful
VPNs are best to go as long as you don’t want any limitations, which means you can browse long-term, along with sensitive data. As said earlier, the VPN offers a secure connection and adds an extra layer of security.
Sending personal information; working on a bank portal over the public internet are some dangerous situations, but enabling VPN on your device makes your information secure. Note that the ones with a heavy price tag are the best option; since you are a person who values privacy initially, the VPN is worth investing in.
If you need help with choices of which VPN is best, you can go through our best VPN for Mac.
What Are Proxy Servers
A proxy server is a middle path between you and a website. Most prominently, the proxy servers are found online. You have to click on them, enter the domain you are willing to go, and it will simply navigate you there.
Proxy works when you give the web address, then it connects it and accordingly loads the corresponding content. The main benefit of using the proxy is that it doesn’t let you connect to the website directly; it works as a center path. I mean that the websites only enable to see Proxy Server IP Address, keeping your device entirely undercover.
When you visit a proxy server site, they ask you to enter the country you want. This is more than originality; they deliberately fool various services and websites.
If you want access to another region’s content, you can firmly access it using the proxy server. This is because the website only sees the location of a proxy server. And that’s the reason it allows you to access the content stuffed in the website.
What Are Different Proxy Server
SOCKS5 Proxies
A SOCKS5 proxy is similar to web proxies or HTTP, but you can connect to websites and applications without an error.
A SOCKS5 proxy restricts data transfer to the 5th layer, smartly restricting attempts to scan or tunnel using the hacking tool.
The program must be compatible if you are setting up to the application level. However, unlike the VPN, it cannot control outgoing and incoming traffic. But it’s best for a user for peer-to-peer file transferring, torrents, email, etc.
Transparent Proxies
It’s a proxy set up on the network to monitor and control website traffic. It’s named transparent since it’s completely unnoticeable. However, it’s mainly used by Offices, Schools, and even cafes to prevent users from accessing the websites.
Benefits Of Proxy Servers
A proxy server can do it quickly if you are willing to unblock the data over the region. There is no need for any installation of extras, have to head to the proxy servers and select the country you want. However, this isn’t a long-term solution but a temporary solution for a problematic website.
As of now and forever, the proxy server is available online, and great thing you can do it over any peripherals.
Drawback Of Proxy Server
Unfortunately, if you are willing to enter the website namelessly, a proxy server isn’t the best to go with. Furthermore, if you are using the proxy servers just for browsing, over time, you will result into aggravating and slow. So, ignore using a proxy if you want to anonymize your multiple websites.
Enter Proxy Server Settings On Mac
If your Mac computer is linked to the local network and the firewall protects it, you must configure a proxy server to access some content. So if you are first time configuring, here are the steps you need to follow.
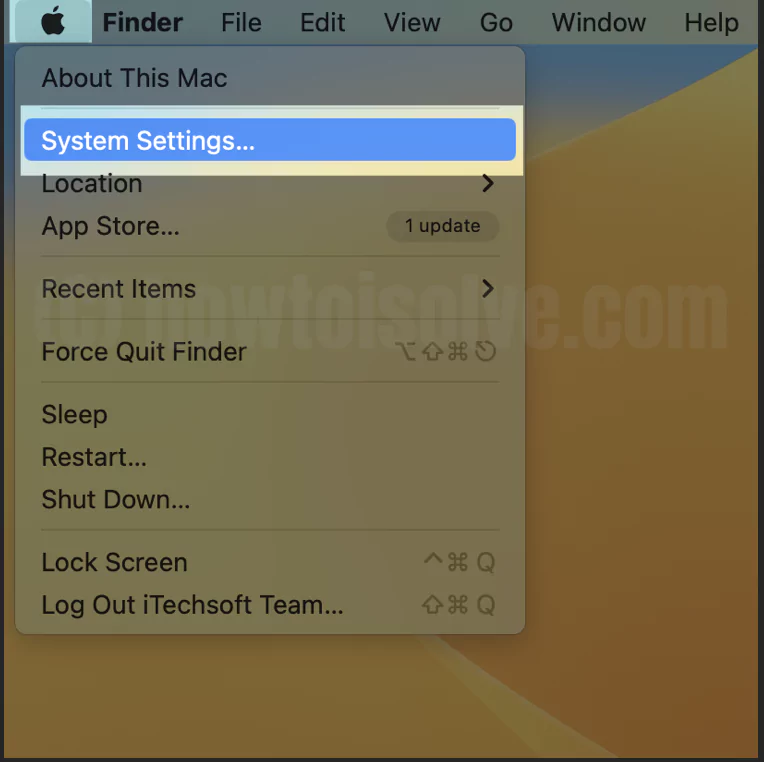
- On the Mac computer, select Apple Menu from the left top corner of the screen. Choose System Settings…
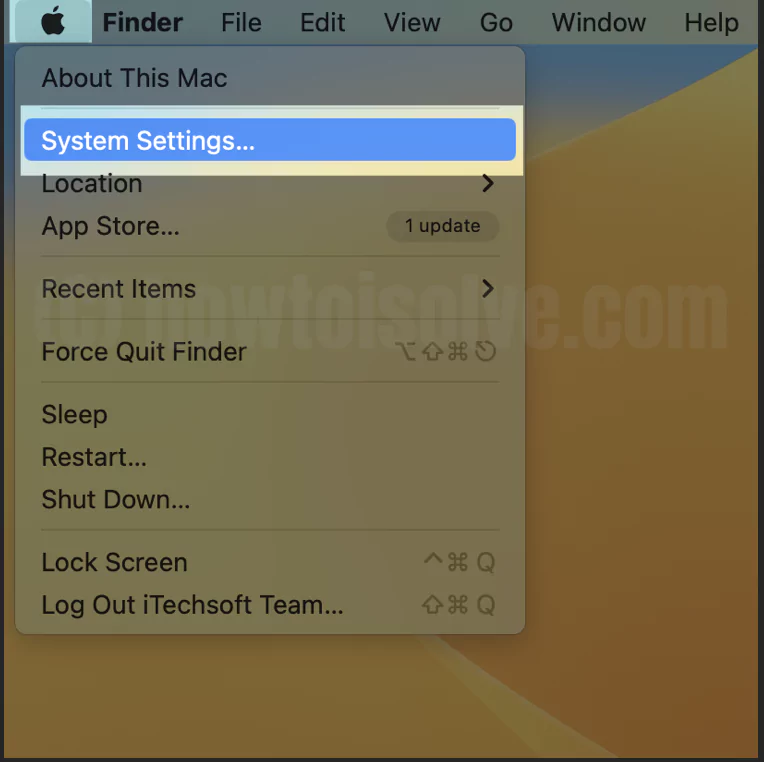
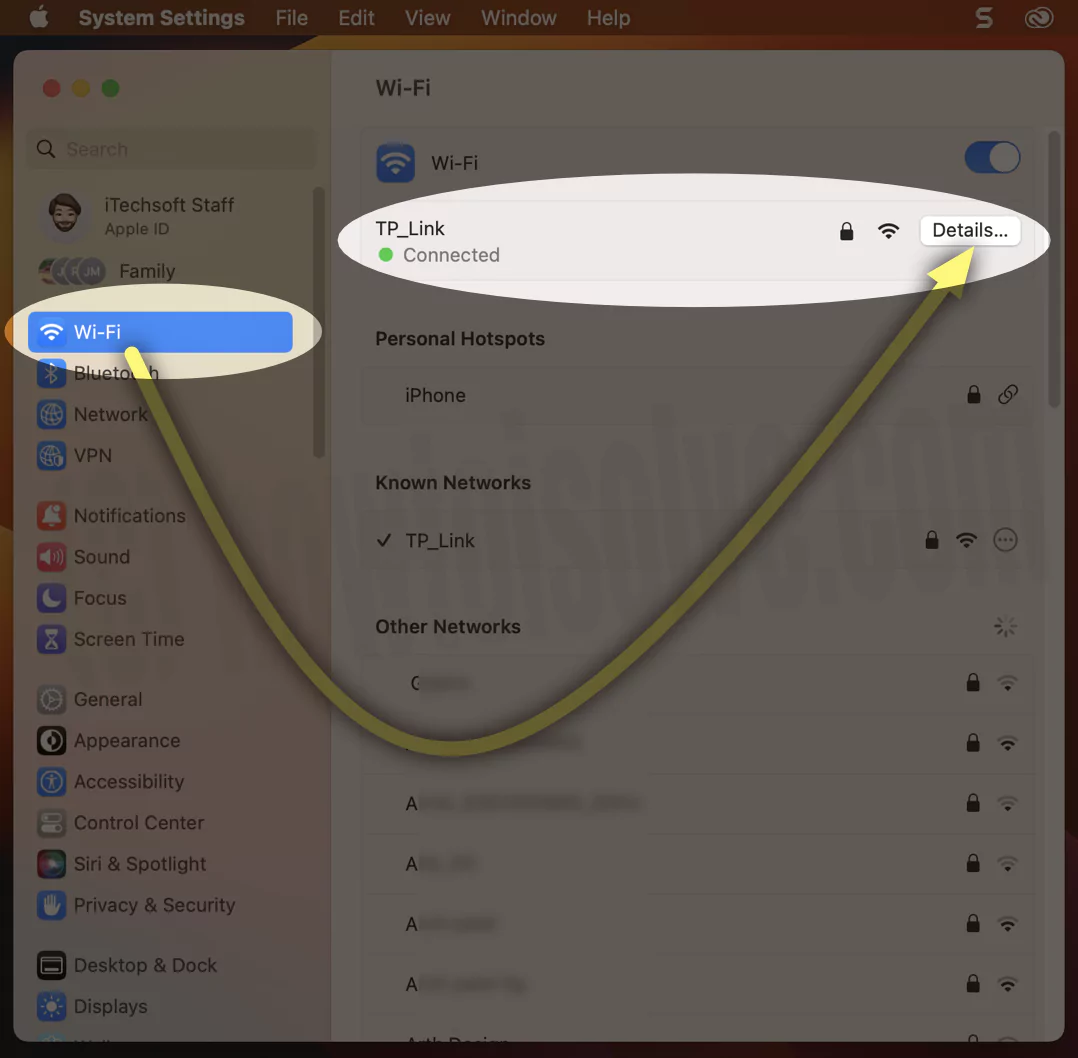
- Select Wi-Fi. Click on Network Services to which you are connected.
- Click on Details… connected WiFi network name next to it.
If you are willing to set it up manually, follow the steps below;
- Enable the Automatic Proxy Discovery
- If the network administrator offers you the address of PAC, enable the Automatic Proxy Configuration”, and write down the address of PAC in the URL field.

If you are always willing to configure the proxy manually, follow the steps below.
- Enable the proxy, then jot down its address and port number.
- If required, enable “Proxy Servers Require Password,” then write the username and password.

6. Hit OK.
What is a VPN?
VPN encrypts what is received and sent from the internet. It helps you, a user, to access website content secretly and privately, regardless of the network you are using.
For instance, it is the safest and most secure courier, transporting website data from one end to the other. Moreover, it hides the IP Address and handily allows you to change the location so you can receive access to the data that’s available in your region. Just like movies or shows on Netflix. The VPN works in the operating system and encrypts all outgoing and incoming internet traffic.
What Are Different Types VPNs
Site-To-Site VPN
A site-to-site VPN is mapped to connect with different geographical regions securely. This type of VPN is visible in most security gateway. Since all traffic from one website to another is passed through this gateway, thus VPN encrypts the traffic sent from the website to a gateway. Further, the gateway decrypts the message or data and moves it to the destination.
Remote Access VPN
A remote access VPN is map to link the remote users with a corporate network. For instance, many companies offer only work from home, and thus they configure secure remote access VPNs from the Client to work on critical operations via corporate sites.
VPN As A Service
VPN as a service is mapped within the cloud-based infrastructure where the message or packets from the Client enter the internet from that cloud infrastructure instead of using the Client’s local address. Note that a consumer uses this model, preventing the users from connecting to the unsecured public internet.
Benefits Of VPN
The VPN is best if you do a task online. On the other hand, the proxy only anonymizes your activity once the data goes to the central server. This means either an ISP or a hacker can spy on your online activity. However, as I said earlier, VPN maps the tunnel; no one can even track your activity.
Ultimately, you are more secure since your data is encrypted even on the public network. You may already be familiar that many clever hackers work 24/7 to steal data, but you don’t need to worry when connected to VPN.
Drawback Of A VPN
The VPN comes with a hefty price tag. And the worst part is there is no best VPN with a cheaper rate. Not only that, as the VPN is design as software, it needs to be installed in your device storage. That’s why, over time, you will encounter the low performance of computers as it encrypts the data before sending.
How To Enable/Disable VPN On Mac
To connect to a VPN on a Mac computer, you must enter the network’s configuration setting. The settings above include; VPN Server Address, Account Name, and Authentication Settings(Password or Settings)
However, if you don’t have or want the information, you can contact the VPN service provider to connect with the VPN service on Mac securely.
You must double-click on the setup if you receive VPN settings as a file.
Note: The steps below are for the latest macOS (macOS Ventura and earlier). For older versions, you can learn by clicking on the Link.
Enter VPN Settings Manually
- On the Mac computer, select Apple Logo > System Settings… Up next, choose VPN from the left side panel.
- VPN Configuration will be added automatically under VPN settings after you install the VPN Program on Mac.

Or
Turn on VPN Using VPN Shortcut from the top Mac menu,

or Select Add VPN Configuration, and then click on the type of VPN you are willing to set up. If your VPN is installed on your Mac, see the installed VPN profile here. Enable the toggle to start VPN.
Otherwise, follow the below manual action to add VPNs…For
L2TP over IPSec…
Cisco IPSec…
IKEv2…

- Rewrite the VPN Service in the Display Name Field.
- If you are configuring an L2TP over IPSec VPN, choose the VPN configuration pop-up, then select a configuration.
- If you want to ignore using Dual VPN, go with the Default Configuration.
- Enter and configure the settings for new VPN services. However, required settings and information vary from VPN services, unlike the server name, the account password, and the administrator name.
- If indeed, jot down the additional settings,
- L2TP over IPSec: You can enter settings for Options, TCP/IP, DNS, and Proxies.
- Cisco IPSec or IKEv2: You can enter settings for DNS and Proxies.
- Click Create.
Create And Modify VPN Settings
- On the Mac computer, navigate to the Apple Logo > System Settings… > VPN.
- Select “i” (Info Button) from the VPN window, located next to the VPN Service you want to cancel.

- If willing, Change Settings.
- Select OK (or Cancel if you do not want to create any changes).
Remove A VPN Configuration
- On a Mac computer, head to the Apple Logo > System Settings… Choose VPN.
- Click on the Info Button beside the VPN Services you are willing to remove.
- Select Remove Configuration, and give further confirmation.
If VPN is not removed from macOS, we need to use a VPN uninstaller. Must read this on how to uninstall VPN on Mac.
There is no debate when there is a choice between a VPN and a Proxy. It prominently depends on your work and browsing habits. Once you answer it, it’s tough to make a choice.
No, both aim to hide the IP address from the website. But apart from this, VPN encrypts the data you send and receive.
Sometimes the VPN degrades the internet speed even if there is no issue with the internet speed. At the same point, using VPN also consume lots of mobile data, so when Mac is connected to a Mobile Hotspot, you must always ignore using it.
The primary purpose of Proxies is to hide the IP address of any device. Therefore, when accessing the content of any website, the website gets fooled, as they can only see the IP address of Proxies instead of your computer.
When you connect to the internet using the VPN, the service provider only knows that you are connected to the VPN. And when you are connected to the VPN, services only see the IP Address of the VPN instead of your computer. Means your actual IP address couldn’t be tracked.
Tor is more robust than a VPN. It’s almost impossible to trace the computer when connected over Tor. As a result, you can smartly and safely visit websites without any footprint.
Yes, VPN does change the IP Address. When enabling the VPN on a Mac computer, it replaces the Mac IP address with its own.
Yes, VPN overrides the proxy; ever since VPN not only hides the IP Address but also encrypts the web activity you visit frequently.
With the launch of NordVPN’s extension for Microsoft Edge, Google Chrome, and Mozilla Firefox, it combines both VPN and Proxy.
Proxies are mainly used for system optimization and information security against threats. However, they can also work as firewalls and also handle authentication requests.